Game Jam – Use Case No.2: Oops… wrong recipient ?
Unveil the Privacy Threat – that’s how we named the Game Jam (October 7, 2017) we’re going to host together with the Alexander von Humboldt Institute for Internet and Society. It will be fun and serious. And we want you to be part of it.
We will present to you three different use cases with a direct connection to data security and privacy by design. We have invited prominent experts to talk about the importance of data privacy, advise and inspire the participants of the Game Jam. What are the use cases, who are the experts? This is use case No 2.
Use Case 2: Oops… wrong recipient ?
The most common privacy threat in companies arises when an employee accidentally sends personal information about somebody else to the wrong recipient.
This may sound like a no-brainer, but in fact, it is one of the biggest challenges in implementing effective privacy protection policies within companies.
There are two typical constellations that give rise to slightly different challenges for companies trying to mitigate this threat:
In the first constellation, an employee uses an email client, and in the second constellation, he/she grants access to a file depository.
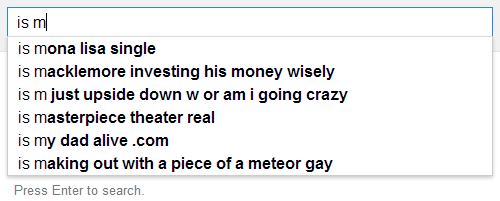
In both cases, an employee typically sends an email or grants access to a repository to the wrong recipient – because the email client or repository incorrectly autocompletes the address based on the first few letters.
The employee forgets to double-check the name and… oops, the information is sent to the wrong recipient.
But there are differences between the cases: They refer to how such an employee can react. If the employee has granted access to a file repository, in principle, he or she can still restrict access retrospectively.

In contrast, if the employee has sent an email, the information is definitely “gone”, and he or she can only ask the recipient not to read and/or open the content.
However, in both cases employees often do not react at all, or they do not appropriately, because they fear negative consequences if his or her colleagues or superior find out about it.
Assignment
The goal of this use case is to develop an engaging game concept that reduces the privacy threat as a result of sending personal information to the wrong recipient, in a playful manner. One target group of such a game are employees in companies dealing with personal data in general.
Want to join the Unveil the Privacy Threat Game Jam on October 7, 2017 in Berlin? Register here for free.
The best game idea will be awarded by an expert jury with an exciting prize – a weekend trip to London for the whole winning team including a visit of The Crystal, the world’s largest museum on the future of (smart) cities – sponsored by Siemens. Furthermore, amongst all participants, we give away two one-year-memberships of Adobe Creative Cloud sponsored by Adobe.*
*without possibility of recourse to legal action
Text by Max von Grafenstein
